In this post, we will explore how Generative AI is transforming on-site search capabilities, enhancing user experiences, and streamlining access to information. We’ll also delve into some of the challenges that come with integrating this advanced technology into existing systems.
Introduction to Onsite Search
Onsite search refers to the functionality on websites that allows users to enter search queries and retrieve information or products within that particular website. This tool is crucial for enhancing user experience, especially on e-commerce platforms where finding products quickly and efficiently can significantly impact customer satisfaction and conversion rates. Effective onsite search can mimic the ease and precision of in-person shopping experiences by quickly guiding users to their desired products or information.
However, traditional search functionalities often face challenges such as dealing with synonyms, spelling errors, and understanding the intent behind a user’s query. These limitations can lead to irrelevant search results, a frustrating user experience, and potentially lost sales. Moreover, traditional searches might struggle with indexing and retrieving content in a way that aligns with how users think and search.
For a deeper dive into enhancing onsite search, see my previous articles Onsite Search: The Must-Have Features for a Seamless User Experience | by Albin Issac | Tech Learnings | Medium Selecting a Search Engine for on-site Search — Open Source vs Search as a Service | by Albin Issac | Medium
Overview of Generative AI
Generative AI refers to a subset of artificial intelligence technologies that can generate new content and ideas based on the data it has been trained on. This contrasts with other forms of AI that typically focus on classifying or predicting outcomes based on input data. Generative AI involves advanced machine learning techniques, including natural language processing (NLP) and neural networks, to produce outputs that are not explicitly programmed into the system.
Technologies behind generative AI, such as NLP, enable the AI to understand, interpret, and manipulate human language. Neural networks, particularly deep learning models, allow the AI to process large amounts of data, recognize patterns, and make decisions with minimal human intervention. These capabilities make generative AI particularly valuable for enhancing onsite search because it can understand and interpret the complexities and nuances of human language, predict what users are searching for even with vague or incomplete queries, and generate relevant results even from sparse data inputs.
By leveraging generative AI, websites can overcome many of the traditional challenges associated with onsite search, leading to a more intuitive and satisfying user experience. This is particularly beneficial in e-commerce settings, where the ability to quickly and accurately display products based on user queries can directly influence buying decisions and overall business success.
Search engines have long utilized AI technologies to enhance user experience and deliver more relevant content. Here are several AI-driven features that have been key in revolutionizing search functionalities:
- Smart Snippets: Provide concise previews of content relevant to search queries, offering users quick insights into the content’s relevance without having to click through to the page.
- Automatic Relevance Tuning (ART): This leverages user interaction data to dynamically adjust and refine the relevance of search results, ensuring that users find the most pertinent information based on collective user behaviors.
- Query Suggestions: By analyzing aggregated search data, this feature suggests related queries in real-time as users type, helping them formulate more effective searches and discover content more efficiently.
- Content Recommendations: Utilizing user behavior, previous search histories, and browsing patterns, AI suggests additional relevant content, potentially increasing engagement and time spent on a site.
- Dynamic Navigation Experience: AI algorithms optimize and personalize navigation interfaces based on common user journeys and behaviors, making site navigation more intuitive and user-friendly.
- Image and Video Recognition: Advanced visual recognition technologies enable search engines to index and retrieve images and videos based not just on metadata but on the visual content itself, enhancing the search capabilities for multimedia.
- Document Search: AI enhances the ability to search within documents by recognizing and indexing text from various document formats. This technology enables users to perform deep content searches, finding specific information within large documents or across a collection of documents. AI-driven features like optical character recognition (OCR) and natural language understanding (NLU) are often employed to interpret the content accurately and return relevant results based on the content’s context rather than just keyword matches.
- Sentiment Analysis: Employed by some search engines, this feature analyzes the emotional tone of content, useful for businesses monitoring brand reputation or media sites gauging public sentiment.
- Personalization Engines: These tailor search results and content displays to individual users based on their unique preferences and past interactions, creating a more personalized and relevant browsing experience.
Generative Answering with AI in Search
Generative AI is transforming the landscape of search technology by introducing the advanced capability of generative answering. This innovative approach transcends the conventional mechanisms of search that primarily focus on retrieving data. Instead, it involves the understanding and generation of responses that directly address a user’s queries.
What is Generative Answering?
Generative answering is the capability of AI systems to construct responses from scratch, based on the extensive data they have been trained on. Utilizing models such as GPT (Generative Pre-trained Transformer) and BERT (Bidirectional Encoder Representations from Transformers), this technology grasps queries in a detailed and nuanced manner, delivering precise, context-aware answers.
Key Benefits of Generative Answering in Search
- Direct Answers: Moving beyond traditional search engines that list documents or links, generative answering provides a direct and succinct response to queries, synthesizing information from multiple sources or extrapolating from existing data.
- Natural Language Interaction: This capability fosters a more conversational interaction, allowing users to engage with the AI in a dialogue format where the system understands and responds to follow-up questions or requests for clarification.
- Personalized Responses: The AI customizes responses based on individual user history or preferences, greatly enhancing the relevance and personalization of the search experience.
- Efficiency in Information Discovery: By quickly delivering the specific information users seek, generative answering significantly reduces the time spent navigating through irrelevant results.
Expanded Applications of Generative AI in Onsite Search
- Customer Support: Provides immediate, accurate answers to customer inquiries, streamlining customer service operations without the need for extensive human intervention.
- E-commerce: Enhances product discovery and customer shopping experience by offering detailed product information and tailored recommendations directly in response to user queries.
- Education: Supports an interactive learning environment by instantly responding to student queries with detailed explanations, promoting a more engaging educational experience.
- Content-Based Sites: Significantly improves search and discovery on content-rich platforms such as news sites, blogs, and digital libraries. Generative AI can swiftly analyze large datasets, enabling it to deliver precise answers, recommend related content, and generate content summaries that aid users in efficiently navigating and consuming information.
- AI-Powered Chatbots: These sophisticated chatbots utilize indexed data to conduct meaningful conversations, providing support and information directly through interactive dialogues.
- Content Creation and Augmentation: AI not only helps in creating new content that aligns with current trends and user interests but also optimizes existing content to enhance its discoverability and engagement.
Generative answering, along with these applications, illustrates the profound impact Generative AI has on enhancing the functionality and user experience of search systems. As this technology continues to evolve, its integration into search platforms is expected to redefine the norms of how information is queried and retrieved, making searches more intuitive, interactive, and effective.
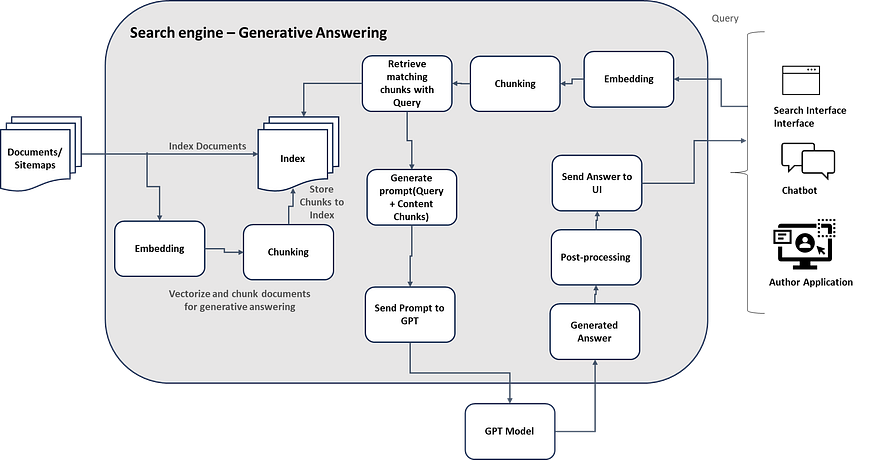
Most of search engines now support Generative AI capabilities to enable Generative Answering and chatbots, the search engines already have customer data indexed through a traditional approach but now the search engines started supporting the Retrieval Augmented Generation approach to enable generative AI capabilities. The content indexing and retrieval process is enabled with additional steps to support Generative Answering.
High-Level Steps in Indexing and Retrieval to Support Generative Answering:
1. Document Indexing and Embedding Generation: Before any search queries are processed, documents must be indexed. As part of this indexing process, each document is processed to generate embeddings. These embeddings, which are dense vector representations of the document’s content, capture the semantic essence of the text. Using AI models such as BERT or GPT, the search engine converts the text of each document into these embeddings and stores them in the search index. This allows for efficient retrieval based on semantic similarity rather than mere keyword matching.
2. Query Reception and Preprocessing: When a query is received, the first step is preprocessing. This involves normalizing the text by converting it to lowercase, removing punctuation, and correcting any typos. Such preprocessing simplifies the text to ensure more effective subsequent analysis.
3. Query Embedding Generation: The preprocessed query is then converted into an embedding using the same AI models used during document indexing. This ensures that the query can be semantically compared to the indexed documents.
4. Chunking and Contextual Analysis: If the query is complex or contains multiple elements, it is broken down into smaller chunks. This chunking isolates specific aspects of the query for more targeted processing. Contextual analysis is also performed, considering previously indexed information, user’s search history, or the specific session context.
5. Retrieval from Index: The query embedding is used to retrieve the most relevant documents from the search index. This is done using similarity metrics that compare the query’s embedding with the embeddings of documents stored in the index, ensuring the retrieval of content that matches the semantic intent of the query.
6. Generate Prompting: After relevant information is retrieved, the search engine constructs a detailed prompt for the generative model. This prompt includes the query, relevant context from the retrieved documents, and additional pertinent information that can guide the AI in generating an accurate response.
7. Send Prompt to Generative Model: This prompt is sent to a generative AI model, such as GPT-3 or GPT-4, which uses it to generate a response that directly answers the user’s query. The generative model synthesizes the information, producing coherent, context-aware text.
8. Answer Generation and Post-Processing: The generated answer undergoes post-processing to ensure it meets quality standards, refining it for clarity and appropriateness. If necessary, the prompt may be adjusted and the generation process rerun.
9. Delivery to User: The refined answer is then delivered to the user through an interface that may allow further interactions, such as query refinement, follow-up questions, or feedback. This feedback is crucial for continuous learning and system improvement.
The integration of Generative AI into search engines represents a paradigm shift away from traditional keyword-centric approaches towards more dynamic, context-sensitive systems. This advancement enriches the search experience, providing users with direct answers, engaging conversations, and tailored content, thereby refining the information discovery process.
Most onsite search engines have now adopted Generative AI capabilities. The advantage here is that since data has already been indexed using traditional methods, implementing Generative AI is relatively straightforward, avoiding the need for extensive content reprocessing and the setup of Retrieval Augmented Generation (RAG) workflows. Furthermore, these search engines offer APIs that facilitate the retrieval of data for both traditional search results and generative answering, making it possible to display information through various interfaces like search pages, chatbots, and more.
A concern with this approach, however, is that many search engine systems offer limited flexibility in selecting embedding models, configuring chunking, or choosing the GPT model. They often rely on predefined proprietary or open-source models, configurations, and prompts. This can be problematic for those who require more control over data processing and the customization of prompts and models.
The capacity for Generative AI to deliver quick and direct answers to customers is an impressive feature that significantly enhances user interaction. Looking forward, there is an anticipation that search engines will begin to provide greater flexibility and options to meet custom requirements for generative answering, catering to a wider range of use cases and further innovating the field of search.
Refer to About Relevance Generative Answering (RGA) | Coveo Machine Learning for understanding how Coveo supports Generative Answering